Hi Professor! I caught an error in my submission and have fixed it.
I’m hoping that you can take the corrected markdown below as my final
submission. Sorry for the inconvenience! -Addie Muller
https://hackmd.io/@addiemuller23/HJDF1qDWs
Web Search and Evaluation
Google Search
There are many ways to make a Google search more exact, as detailed
by Google’s “Refine
web search” help page. This is where tips and tricks for the search
bar can be learned. For example, to see how many results are on the
English Wikipedia that use exactly the words “Northeastern University,”
search “Northeastern University” including the quotation marks and
specify the site by writing site:en.wikipedia.org. This yields about
5,780 results.

Another example of these advanced search functions is to find the
available web pages for skate fish that do not mention the phrase “ice
rink.” To do this, you would search skate fish and then write -“ice
rink,” again including the quotation marks to ensure that results with
either “ice” or “rink” in them can still show up.

Next, to narrow a search by dates, you search for whatever, click
“tools” under the search bar, and then select “any time” and adjust to
whatever desired. For example, if you are searching for results for
“Northeastern Huskies” from the first day of 2001 to the last day of
2002, you could select “custom range” and then enter those date ranges.
It should read back the dates that you entered under the search bar,
like the image below.

Finally, to narrow an image search you can use the Advanced Google
Image Search, linked here. Let’s say
you’re looking for the top image that shows up for the specific phrase
“penguin pair” and has a “Creative Commons” usage right. The advanced
search should look like the image below and generate this wonderful
photo of two penguins as the top result.


Web Credibility
I question the credibility of this
article written about which celebrities have used the most CO2
emissions while flying their private jets. The article concluded that
Taylor Swift used her private jet the most, amassing 8,293.54 tonnes
between January and July. Whether you’re a fan of Taylor Swift or not,
it’s important to put bias aside and use our “critical thinking skills
to judge the reliability and credibility” (Valenza) of this news
report.
Following Valenza’s suggestions outlined in “Truth,
truthiness, triangulation: A news literacy toolkit for a ‘post-truth’
world” to check for accuracy, I started by looking into the author.
Phoebe Kowhai doesn’t appear to have any history in environmental
studies or pop culture, giving her little authority to speak on the
subject. She is an Assistant Editor at “The Tab,” a sensationalist site
that closely resembles the tabloids. The story written on celebrity
carbon emissions, other articles written by Kowhai, and the site as a
whole are aiming for an emotional reaction, generated by provocative
headlines. Going back to Valenza’s suggestions, I tried to investigate
the source that Kowhai cited. However, the link led to a marketing agency’s
website, not any specific data collected on the celebrities. The
inability to corroborate sources makes the whole situation even more
suspicious.
As advised by the Berkeley
Library, I also tried to isolate the purpose of this article. The
subheading gives it away, reading “Shocker, Kylie Jenner isn’t even in
the top 10.” Jenner had recently posted about her use of her private jet
to take a 17-minute
flight, which resulted in public backlash. Kowhai’s article aimed to
take the attention off of Jenner and turn it to Swift and the other nine
celebrities featured in the article.
Finally, I need to acknowledge my own search bias. I am a big fan of
Taylor Swift’s music and defend her choices more than I would other
celebrities. However, I feel I remained as neutral as possible in
pointing out the inaccuracies in this article, while also not excusing
celebrities’ gross overuse of private jets.
Wikipedia Evaluation
As per the policy of Wikipedia:Verifiability,
all information must come from a reliable source, and the editor must
demonstrate verifiability by citing reputable sources. In this version
of the Wikipedia page for Joseph
Reagle, it claims that he worked at the World Wide Web Consortium.
This properly cites w3.org, specifically a page on Joseph Reagle’s
involvement. This is a reputable site for information on this
organization, indicated by the .org at the end of the URL. There is more
information referenced on this site with details of Joseph Reagle’s work
history and various organizational involvement, furthering its
credibility.
Another claim made by Reagle’s Wikipedia page was that his book
Good Faith Collaboration was “bestselling.” There was no
provided citation for this claim, which defies Wikipedia’s policy of
Verifiability. While there was a link to another Wikipedia page on
Good Faith
Collaboration, there was no evidence there either that this
book was a bestseller. I took to Google, where I again found no evidence
to support this claim. Therefore, I would call to remove this statement
from the Wikipedia page.
Finally, while I found no other information in this Wikipedia article
that appeared untrue, I did not find a reference for the claim that
“Reagle wrote his Ph.D. thesis on Wikipedia editing, which he described
as stigmergy.” Some digging found that this was an accurate
claim, just with no source to defend it on the Wikipedia site.
This page was created on August 1, 2011, according to the “View
History” tab on Wikipedia. ________________________________ From:
Adeline Muller Sent: Wednesday, September 21, 2022 1:56 PM To: Reagle,
Joseph J.Reagle@northeastern.edu Subject: hackmd: Web Search
and Evaluation
https://hackmd.io/@addiemuller23/HJDF1qDWs
Web Search and Evaluation
Google Search
There are many ways to make a Google search more exact, as detailed
by Google’s “Refine
web search” help page. This is where tips and tricks for the search
bar can be learned. For example, to see how many results are on Google
that use exactly the words “Northeastern University,” search
“Northeastern University,” including the quotation marks. This yields
about 24,200,000 results.

Another example of these advanced search functions is to find the
available web pages for skate fish that do not mention the phrase “ice
rink.” To do this, you would search skate fish and then write -“ice
rink,” again including the quotation marks to ensure that results with
either “ice” or “rink” in them can still show up.

Next, to narrow a search by dates, you search for whatever, click
“tools” under the search bar, and then select “any time” and adjust to
whatever desired. For example, if you are searching for results for
“Northeastern Huskies” from the first day of 2001 to the last day of
2002, you could select “custom range” and then enter those date ranges.
It should read back the dates that you entered under the search bar,
like the image below.

Finally, to narrow an image search you can use the Advanced Google
Image Search, linked here. Let’s say
you’re looking for the top image that shows up for the specific phrase
“penguin pair” and has a “Creative Commons” usage right. The advanced
search should look like the image below and generate this wonderful
photo of two penguins as the top result.


Web Credibility
I question the credibility of this
article written about which celebrities have used the most CO2
emissions while flying their private jets. The article concluded that
Taylor Swift used her private jet the most, amassing 8,293.54 tonnes
between January and July. Whether you’re a fan of Taylor Swift or not,
it’s important to put bias aside and use our “critical thinking skills
to judge the reliability and credibility” (Valenza) of this news
report.
Following Valenza’s suggestions outlined in “Truth,
truthiness, triangulation: A news literacy toolkit for a ‘post-truth’
world” to check for accuracy, I started by looking into the author.
Phoebe Kowhai doesn’t appear to have any history in environmental
studies or pop culture, giving her little authority to speak on the
subject. She is an Assistant Editor at “The Tab,” a sensationalist site
that closely resembles the tabloids. The story written on celebrity
carbon emissions, other articles written by Kowhai, and the site as a
whole are aiming for an emotional reaction, generated by provocative
headlines. Going back to Valenza’s suggestions, I tried to investigate
the source that Kowhai cited. However, the link led to a marketing agency’s
website, not any specific data collected on the celebrities. The
inability to corroborate sources makes the whole situation even more
suspicious.
As advised by the Berkeley
Library, I also tried to isolate the purpose of this article. The
subheading gives it away, reading “Shocker, Kylie Jenner isn’t even in
the top 10.” Jenner had recently posted about her use of her private jet
to take a 17-minute
flight, which resulted in public backlash. Kowhai’s article aimed to
take the attention off of Jenner and turn it to Swift and the other nine
celebrities featured in the article.
Finally, I need to acknowledge my own search bias. I am a big fan of
Taylor Swift’s music and defend her choices more than I would other
celebrities. However, I feel I remained as neutral as possible in
pointing out the inaccuracies in this article, while also not excusing
celebrities’ gross overuse of private jets.
Wikipedia Evaluation
As per the policy of Wikipedia:Verifiability,
all information must come from a reliable source, and the editor must
demonstrate verifiability by citing reputable sources. In this version
of the Wikipedia page for Joseph
Reagle, it claims that he worked at the World Wide Web Consortium.
This properly cites w3.org, specifically a page on Joseph Reagle’s
involvement. This is a reputable site for information on this
organization, indicated by the .org at the end of the URL. There is more
information referenced on this site with details of Joseph Reagle’s work
history and various organizational involvement, furthering its
credibility.
Another claim made by Reagle’s Wikipedia page was that his book
Good Faith Collaboration was “bestselling.” There was no
provided citation for this claim, which defies Wikipedia’s policy of
Verifiability. While there was a link to another Wikipedia page on
Good Faith
Collaboration, there was no evidence there either that this
book was a bestseller. I took to Google, where I again found no evidence
to support this claim. Therefore, I would call to remove this statement
from the Wikipedia page.
Finally, while I found no other information in this Wikipedia article
that appeared untrue, I did not find a reference for the claim that
“Reagle wrote his Ph.D. thesis on Wikipedia editing, which he described
as stigmergy.” Some digging found that this was an accurate
claim, just with no source to defend it on the Wikipedia site.
This page was created on August 1, 2011, according to the “View
History” tab on Wikipedia.

 I
implemented a second rule to filter out emails from The Fashion Society,
so I have all of the club’s communications in one place.
I
implemented a second rule to filter out emails from The Fashion Society,
so I have all of the club’s communications in one place.












 The
first time I downloaded Tik
The
first time I downloaded Tik



 )
)

















 Within the prisoner metaphor, if you were to
cooperate but your partner defected, you would receive four years in
prison, while they only get one. If you both defect, you both get three
years (which is wholeheartedly undesirable as you know if you both
cooperate there is a better outcome). And yet, why do people feel
inclined to NOT cooperate?
Within the prisoner metaphor, if you were to
cooperate but your partner defected, you would receive four years in
prison, while they only get one. If you both defect, you both get three
years (which is wholeheartedly undesirable as you know if you both
cooperate there is a better outcome). And yet, why do people feel
inclined to NOT cooperate?
 As
many of my communication classes talk about the internet in some context
eventually, almost every single time we look at this picture. Even
though we do not really know who someone is at first glance,
somehow in some way something can always get connected back to the
person who originally posted something.
As
many of my communication classes talk about the internet in some context
eventually, almost every single time we look at this picture. Even
though we do not really know who someone is at first glance,
somehow in some way something can always get connected back to the
person who originally posted something.
 Even the small bio on her website has the phrase “I’m a black,
international photo model and I have the biggest breasts in Europe.”
However, as seen by this next image, she is obviously not black.
Even the small bio on her website has the phrase “I’m a black,
international photo model and I have the biggest breasts in Europe.”
However, as seen by this next image, she is obviously not black.  Martina has
oversexualized herself through the guise of being a black woman.
Therefore, she profits off of their suffering when she truthfully has no
idea what it is like. Similarly, but not to the same exact extreme,
Martina has
oversexualized herself through the guise of being a black woman.
Therefore, she profits off of their suffering when she truthfully has no
idea what it is like. Similarly, but not to the same exact extreme, 

 We can see that one person has intentionally
clicked the “helpful” button, letting everyone else know they found this
review to be helpful. However, what encouraged Heather to comment in the
first place? As
We can see that one person has intentionally
clicked the “helpful” button, letting everyone else know they found this
review to be helpful. However, what encouraged Heather to comment in the
first place? As  Immediately, my one friend joked about not wanting to like my post since
I did not like his. This, in a way, was my own Instagram Pod. Despite
the fact that the articles for this response were written in 2015 and
2018, the concepts still remain applicable to today. Social media truly
emphasizes exchanges in interaction rather than it being a way to share
more about your life.
Immediately, my one friend joked about not wanting to like my post since
I did not like his. This, in a way, was my own Instagram Pod. Despite
the fact that the articles for this response were written in 2015 and
2018, the concepts still remain applicable to today. Social media truly
emphasizes exchanges in interaction rather than it being a way to share
more about your life. We can
clearly see one banner ad, one ad inside the article itself, and two ads
on the side.
We can
clearly see one banner ad, one ad inside the article itself, and two ads
on the side. The
banner ad, the ad within the content itself and one of two of the side
ads disappeared with the ad blocker. While the ad blocker did not get
rid of 100% of the ads, it certainly made the viewing and reading
experience of this article much better. I did not feel as visually
overwhelmed when using the ad blocker.
The
banner ad, the ad within the content itself and one of two of the side
ads disappeared with the ad blocker. While the ad blocker did not get
rid of 100% of the ads, it certainly made the viewing and reading
experience of this article much better. I did not feel as visually
overwhelmed when using the ad blocker.







 3. Custom
Range…From 1/1/2001 To 12/31/2002
3. Custom
Range…From 1/1/2001 To 12/31/2002  4. Result:
4. Result:
 ** Find me the
top image of the exact phrase “penguin pair” with a “Creative Commons”
usage right.
** Find me the
top image of the exact phrase “penguin pair” with a “Creative Commons”
usage right. 3. Then narrow your
results by… usage rights: Creative Commons licenses
3. Then narrow your
results by… usage rights: Creative Commons licenses  4. Top image:
4. Top image:























































































































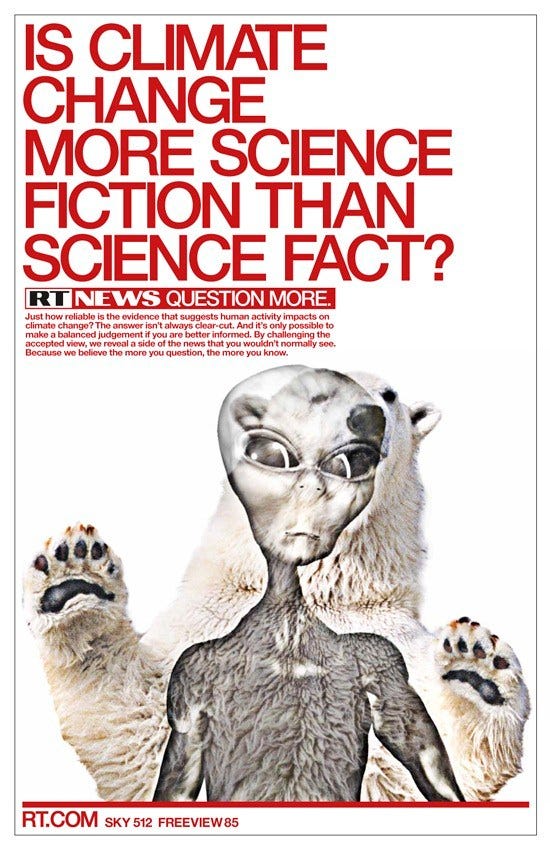
 I saw this as a similar concept
to the filter bubble mentioned in the article. The only difference was
that we are inputting the filters manually. This was something we
learned to do in our last mandatory assignment. I think this type of
manual filtering is effective in a different way than the filter bubbles
are. The filter bubbles create the feed that you are expecting to see
and the manual filters further act upon that. The first source,
“Understanding Information Disorder” by Claire Wardle, brought into
account the sharing of misinformation. Misinformation in this case, was
described as when real information is presented in a way that it
suggests something false. This misinformation is something that I would
see it being effective to filter out. “Did Media Literacy Backfire?” by
Danah Boyd is another source where the influence of the internet is
explored. It is mentioned here how the miss use of sources that are not
considered trustworthy can lead to people being miss-informed. The
automatic filtering out of these sources would most certainly makes for
a more streamlined and effective internet experience. These 3 sources
together allowed me to get a deeper view into what we looked into in our
last mandatory assignment in terms of crap detection, and allowed me to
get deeper insight into the idea of filtering online.
I saw this as a similar concept
to the filter bubble mentioned in the article. The only difference was
that we are inputting the filters manually. This was something we
learned to do in our last mandatory assignment. I think this type of
manual filtering is effective in a different way than the filter bubbles
are. The filter bubbles create the feed that you are expecting to see
and the manual filters further act upon that. The first source,
“Understanding Information Disorder” by Claire Wardle, brought into
account the sharing of misinformation. Misinformation in this case, was
described as when real information is presented in a way that it
suggests something false. This misinformation is something that I would
see it being effective to filter out. “Did Media Literacy Backfire?” by
Danah Boyd is another source where the influence of the internet is
explored. It is mentioned here how the miss use of sources that are not
considered trustworthy can lead to people being miss-informed. The
automatic filtering out of these sources would most certainly makes for
a more streamlined and effective internet experience. These 3 sources
together allowed me to get a deeper view into what we looked into in our
last mandatory assignment in terms of crap detection, and allowed me to
get deeper insight into the idea of filtering online.



















 [](
[](













 Spokeo
Spokeo







 [Filter
Bubbles](
[Filter
Bubbles](






 These are fairly in keeping
with my interests
These are fairly in keeping
with my interests This section made me laugh, as
I have been heavily shopping for a new pair of shoes and Taylor Swift
concert tickets recently
This section made me laugh, as
I have been heavily shopping for a new pair of shoes and Taylor Swift
concert tickets recently



























 As displayed in the
before and after photos, the main Best Buy banner app was successfully
blocked by the ad blocker Ublock Origin, but the trending videos pop-up
ad within the Allrecipes site was not blocked.
As displayed in the
before and after photos, the main Best Buy banner app was successfully
blocked by the ad blocker Ublock Origin, but the trending videos pop-up
ad within the Allrecipes site was not blocked.
 The ad blocker was
incredibly effective in blocking ads on Easybib as the banner ads and
ads on the side of the page are completely eliminated, including
Easybib’s own ad video.
The ad blocker was
incredibly effective in blocking ads on Easybib as the banner ads and
ads on the side of the page are completely eliminated, including
Easybib’s own ad video.
 The ad blocker was able
to block all the ads on the right side of the video, as well as the ad
embedded within the youtube video.
The ad blocker was able
to block all the ads on the right side of the video, as well as the ad
embedded within the youtube video.























 Here is the top image
of a penguin pair with creative commons
Here is the top image
of a penguin pair with creative commons















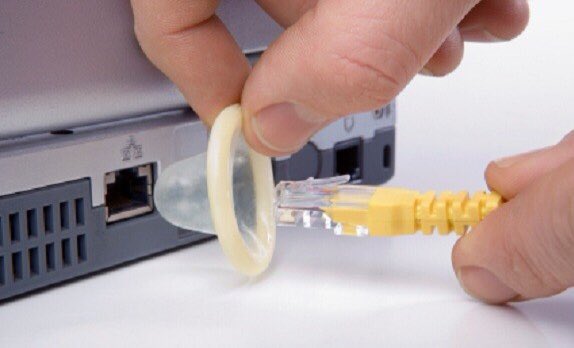
 After the Data Breach
event that exposed the information of 530 million Facebook users, data
leak is something that I am always scared of when I use the internet. Of
course, I don’t want my sensitive data to be accidentally exposed
physically, on the Internet, or in any other form including lost hard
drives or laptops. But I still have to use the internet daily. As a
result, I’d like to learn how HTTPS works to protect my data from a
cybercriminal, what I can do as a user to protect myself while using the
internet, and how TCP/IP, DNS, and HTTP work together as a chain.
Furthermore, as an international student, those “internet terms” are
always difficult for me to remember and comprehend. Thus, I would love
to know if there is a simpler way to prepare for this, such as imagining
how it would work in a real-life situation would be extremely beneficial
in this case.
After the Data Breach
event that exposed the information of 530 million Facebook users, data
leak is something that I am always scared of when I use the internet. Of
course, I don’t want my sensitive data to be accidentally exposed
physically, on the Internet, or in any other form including lost hard
drives or laptops. But I still have to use the internet daily. As a
result, I’d like to learn how HTTPS works to protect my data from a
cybercriminal, what I can do as a user to protect myself while using the
internet, and how TCP/IP, DNS, and HTTP work together as a chain.
Furthermore, as an international student, those “internet terms” are
always difficult for me to remember and comprehend. Thus, I would love
to know if there is a simpler way to prepare for this, such as imagining
how it would work in a real-life situation would be extremely beneficial
in this case. Cramming or mass
practice is a favorite study method for many college students, including
myself! Even though I know it’s bad for me and that I’ll forget
everything the moment I leave the exam room, I can’t stop myself from
doing it. But deep down, I always have the feeling that I can do better.
Especially after my first Co-op, I feel like I need to change my study
method to learn more efficiently. Like Brown said in the article, if you
practice elaboration, there’s no known limit to ’how much you can learn.
But practice takes time, so I will try my best to do it step by step
from now on.
Cramming or mass
practice is a favorite study method for many college students, including
myself! Even though I know it’s bad for me and that I’ll forget
everything the moment I leave the exam room, I can’t stop myself from
doing it. But deep down, I always have the feeling that I can do better.
Especially after my first Co-op, I feel like I need to change my study
method to learn more efficiently. Like Brown said in the article, if you
practice elaboration, there’s no known limit to ’how much you can learn.
But practice takes time, so I will try my best to do it step by step
from now on. When I was younger, I
used to get so frustrated every time I had to click on the “stop showing
me this ad” button because Google would always be like, “Oops, nah, I
don’t believe I will.” Then, in the Fall of 2021, I did my first Co-op
at Ogilvy where I got to use cookies and databases provided by our
client to advertise products. It blew my mind. For marketers, these
things are beneficial to ensure that we can reach our target markets and
reach the right people. Because seeing irrelevant ads is pointless for
both the firm and the viewer. Thus, if we look at the situation in a
positive light, if we had to view advertising every day whether we want
to or not, wouldn’t it be much better if it was for things we truly
wanted or were interested in? Just last week, I was on the phone with a
friend talking about how I’ve been craving Malatang, a Chinese street
food, but don’t know where to get it. The next day, a Malatang
restaurant was recommended to my friend and me on our TikTok so we
wouldn’t have to seek it ourselves. Moreover, by gathering your
information, entertainment platforms such as TikTok, YouTube, and
Facebook may better propose content that is more appropriate to your
preferences. Isn’t that wonderful? To conclude, I do believe that
internet privacy is a major concern and that we, as customers, should be
informed about it before making any decisions. However, everything has
two sides, and we as rational internet users should always consider both
sides of a situation before making any final judgment in our life.
When I was younger, I
used to get so frustrated every time I had to click on the “stop showing
me this ad” button because Google would always be like, “Oops, nah, I
don’t believe I will.” Then, in the Fall of 2021, I did my first Co-op
at Ogilvy where I got to use cookies and databases provided by our
client to advertise products. It blew my mind. For marketers, these
things are beneficial to ensure that we can reach our target markets and
reach the right people. Because seeing irrelevant ads is pointless for
both the firm and the viewer. Thus, if we look at the situation in a
positive light, if we had to view advertising every day whether we want
to or not, wouldn’t it be much better if it was for things we truly
wanted or were interested in? Just last week, I was on the phone with a
friend talking about how I’ve been craving Malatang, a Chinese street
food, but don’t know where to get it. The next day, a Malatang
restaurant was recommended to my friend and me on our TikTok so we
wouldn’t have to seek it ourselves. Moreover, by gathering your
information, entertainment platforms such as TikTok, YouTube, and
Facebook may better propose content that is more appropriate to your
preferences. Isn’t that wonderful? To conclude, I do believe that
internet privacy is a major concern and that we, as customers, should be
informed about it before making any decisions. However, everything has
two sides, and we as rational internet users should always consider both
sides of a situation before making any final judgment in our life. As Joseph Reagle
detailed in Reading the Comments Chapter 3: “Manipulated: Which Ice Cube
is the Best?”,“10 to 30 percent of online reviews are fake. The cast of
manipulators includes fakers (those who deceptively praise their own
works or pillory others’), makers (those who will do so for a fee), and
the takers (those who avail themselves of such services).” During my
first Co-op, I was one of those makers. Specifically, I was interning at
Ogilvy agency, where one of my duties was to pretend to be a mother who
uses Nuti Food’s milk for her newborn child and reviews the company’s
product for other mothers on Facebook.
As Joseph Reagle
detailed in Reading the Comments Chapter 3: “Manipulated: Which Ice Cube
is the Best?”,“10 to 30 percent of online reviews are fake. The cast of
manipulators includes fakers (those who deceptively praise their own
works or pillory others’), makers (those who will do so for a fee), and
the takers (those who avail themselves of such services).” During my
first Co-op, I was one of those makers. Specifically, I was interning at
Ogilvy agency, where one of my duties was to pretend to be a mother who
uses Nuti Food’s milk for her newborn child and reviews the company’s
product for other mothers on Facebook.






 After read
After read


 This set of ads are interesting
because all three of them are for Canva. I have used Canva very recently
to create a slide presentation for class, but they always attempt to
promote their premium subscription, which unlocks multiple templates and
other ailments.
This set of ads are interesting
because all three of them are for Canva. I have used Canva very recently
to create a slide presentation for class, but they always attempt to
promote their premium subscription, which unlocks multiple templates and
other ailments.
 Once I installed uBlock origin,
the spaces the ads once took up became empty. I was honestly slightly
expecting the size of the clickable articles to change, but everything
remained the same.
Once I installed uBlock origin,
the spaces the ads once took up became empty. I was honestly slightly
expecting the size of the clickable articles to change, but everything
remained the same. 




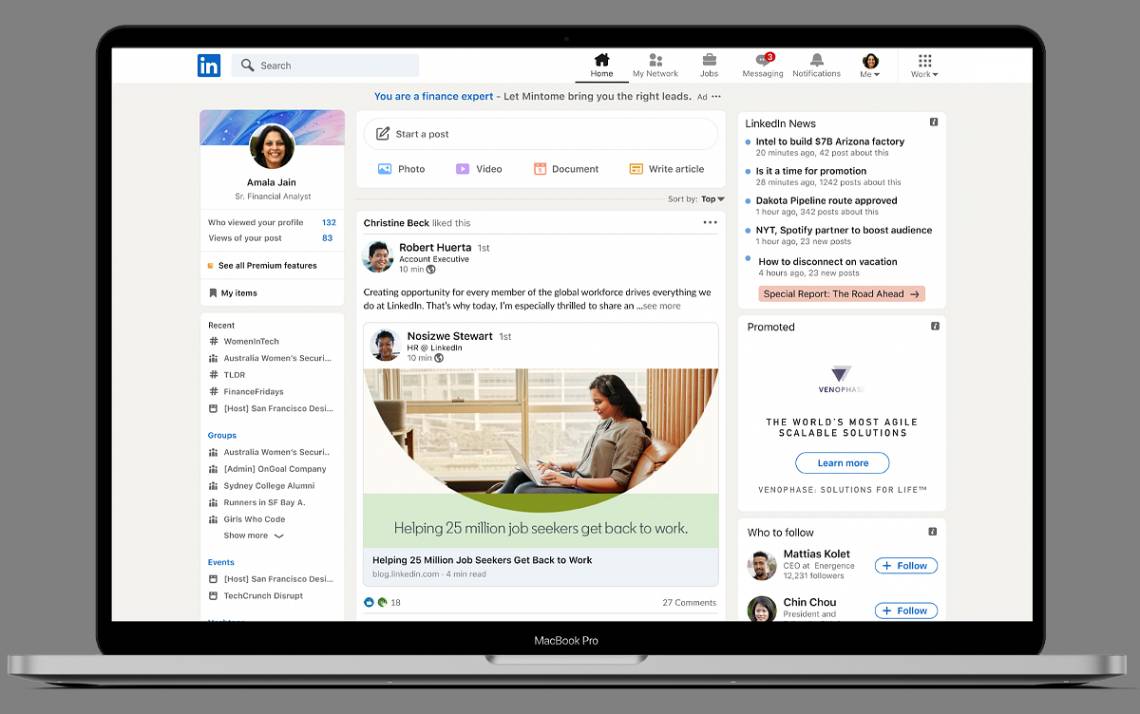
 This part of the assignment
specifically reminded me of what Kernighan mentions in “Understanding
the Digital World” that we essentially use these different types of
media – LinkedIn, Instagram, Tiktok, Google – all for different parts of
our lives. We should think more about how much we contribute to
our own loss of privacy. Shown in the pictures here, I keep my ad center
on Google turned on, allow all content to be saved (and possibly sold by
said companies) on YouTube, Gmail, and many other applications on my
computer. “Third-party” apps also save my content and have access to
that data as well. This help me look for jobs, so when I put in my
interests when I created a profile, it saved them and recommended
similar postings to the job interests I selected.
This part of the assignment
specifically reminded me of what Kernighan mentions in “Understanding
the Digital World” that we essentially use these different types of
media – LinkedIn, Instagram, Tiktok, Google – all for different parts of
our lives. We should think more about how much we contribute to
our own loss of privacy. Shown in the pictures here, I keep my ad center
on Google turned on, allow all content to be saved (and possibly sold by
said companies) on YouTube, Gmail, and many other applications on my
computer. “Third-party” apps also save my content and have access to
that data as well. This help me look for jobs, so when I put in my
interests when I created a profile, it saved them and recommended
similar postings to the job interests I selected.















 Spokeo:
Spokeo:  Ads: no brands or
topics chosen for me
Ads: no brands or
topics chosen for me - Another way to narrow one’s
Google search is to use advance shortcuts. For example, if one wanted to
see webpages about skate fish but none about an ice rink, they could put
“skate fish” in quotation marks but a “-” before “ice rink”. -
- Another way to narrow one’s
Google search is to use advance shortcuts. For example, if one wanted to
see webpages about skate fish but none about an ice rink, they could put
“skate fish” in quotation marks but a “-” before “ice rink”. -  - In order to query to see Web
pages about the Northeastern Huskies from the first day of 2001 through
the last day of 2002, one can plug in “Northeastern Huskies” into the
traditional google search bar, and narrow the results to the specific
date frame. -
- In order to query to see Web
pages about the Northeastern Huskies from the first day of 2001 through
the last day of 2002, one can plug in “Northeastern Huskies” into the
traditional google search bar, and narrow the results to the specific
date frame. - 
































 Also, a variety of
events occur when the client sends a request to the server. TCP/IP, DNS,
and HTTP, for example, all play a role. However, when you request to
access a website, it must transit via several different networks, any of
which might possibly be exploited to eavesdrop or interfere with your
connection.
Also, a variety of
events occur when the client sends a request to the server. TCP/IP, DNS,
and HTTP, for example, all play a role. However, when you request to
access a website, it must transit via several different networks, any of
which might possibly be exploited to eavesdrop or interfere with your
connection. 










 Preferences.
Preferences.